Page History
i2b2 Release 1.7.10
| Anchor | ||||
|---|---|---|---|---|
|
Release Date: April 27, 2018
Release Summary
| Anchor | ||||
|---|---|---|---|---|
|
Release 1.7.10 contains many new enhancements to the i2b2 kernel, many of which improve the security around signing into the i2b2 Web Client. We have included some Auditing features like logging all successful and attempted logins into the i2b2 Web Client or keeping a log of all the Admin functions performed with the Admin Module.
Installation Notes
| Anchor | ||||
|---|---|---|---|---|
|
This release note applies to you if you are upgrading your i2b2 to 1.7.10 from and earlier 1.7.xx version of the i2b2 software. Please see the Upgrade Notes section for any information that is specific to the upgrade process.
If you are installing a new instance of the i2b2 we recommend you refer to the i2b2 Installation Guide found on the i2b2 Community Wiki. This documentation will guide you through the entire installation process. If you run into issues or have questions you can reach out to the community by joining and emailing the google group called i2b2 Install Help.
SHRINE Networks
| Anchor | ||||
|---|---|---|---|---|
|
| UI Text Box | ||||
|---|---|---|---|---|
| ||||
Release 1.7.10 has not been tested within a SHRINE network. Therefore, i2b2 Release 1.7.10 should not be installed within a SHRINE network. It can be installed independently of SHRINE. However because it has not been tested with SHRINE we can not guarantee all of the new enhancements will continue to work correctly when implemented within a SHRINE environment. |
Upgrade Notes
| Anchor | ||||
|---|---|---|---|---|
|
The following i2b2 components contain changes in release 1.7.10.
- i2b2 Database
- i2b2 Server (kernel)
- i2b2 Web Client
The list of changes made can be found in the change summary
Now provide an upgrade path for those sites that do not want to do a whole new install of the i2b2 server. provide just the JAR / war files
page that contains all the upgrade information is: Upgrade to latest version
Database Changes
| Anchor | ||||
|---|---|---|---|---|
|
Release 1.7.10 involves a few changes to the i2b2 Database. Some are simple an addition to the sample data that is included in the demo data that is delivered with the software while others are changes to the database structure to support new features that are included in 1.7.10
Crcdata Tables
QT_BREAKDOWN_PATH
- Added new breakdowns for the new SQL Query Breakdown feature
QT_QUERY_RESULT_TYPE
- Added new breakdowns for the new SQL Query Breakdown feature
- Added new column to support roles based access for the new SQL Breakdowns
- New column name = QT_ROLE_CD
Pmdata Tables
PM_USER_LOGIN table
- Remove the primary key
- add an index PM_USER_LOGIN_IDX
Change Summary - i2b2 Kernel (Core Software) - Release 1.7.10
| Anchor | ||||
|---|---|---|---|---|
|
New Features and Improvements
Additional information about each of these features can be found in the Details about New Features in Release 1.7.10 section located after the Change Summary section for the Web Client.
| Jira | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Bug Fixes
| Jira | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Change Summary - i2b2 Web Client Software - Release 1.7.10
| Anchor | ||||
|---|---|---|---|---|
|
New Features and Improvements
Additional information about each of these features can be found in the Details about New Features in Release 1.7.10 section located after this section.
| Jira | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Bug Fixes
| Jira | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Details about New Features in Release 1.7.10
| Anchor | ||||
|---|---|---|---|---|
|
Many improvements in 1.7.10; grouped into 4 categories
Auditing improvements
| Anchor | ||||
|---|---|---|---|---|
|
The auditing improvements category contains two new features where the i2b2 now logs all attempts to sign onto the i2b2 Web Client and logs all activity within the i2b2 Admin module.
| UI Text Box | ||
|---|---|---|
| ||
The auditing improvements are strictly server and database security enhancements to capture the information for auditing purposes. The audit information is logged in the PM_USER_LOGIN table for both features. Due to different security requirements on who can access this type of database information we have chosen to not include a way for i2b2 users to view or print the audit information from within the i2b2. This decision may be reviewed again for a future release. For now, if a site wants to obtain the logged information they can query their i2b2 database and retrieve the information directly from the PM_USER_LOGIN table. |
Log number of attempted logins
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-285
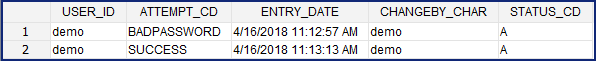
All successful and failed login attempts to sign into the i2b2 Web Client will be logged in the PM_USER_LOGIN table.
Highlights
- No additional setup is needed to turn the enhancement on
- Even when a user is locked out the system will log when they attempt to access the system
Sample of logins from PM_USER_LOGIN
Log Admin Functions
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-286
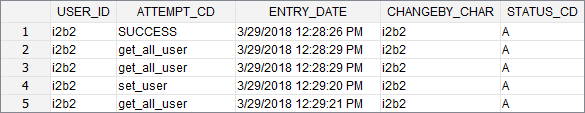
Functions performed within the Admin module will be logged within the PM_USER_LOGIN table.
| Example Box |
|---|
ExampleFor the purpose of this documentation the basic steps an i2b2 Admin takes to add a new user are outlined below: Step 1: Signs into the i2b2 Web Client & selects the Administrator project Step 2: Selects Manager Users from the Navigation Panel Step 3: Clicks on the Add User button Step 4: Enters the information about the user and clicks on Save. Step 5: Clicks on Manage Users to refresh the list and display the new user.
As each steps was performed, the service and USER_ID was logged in the PM_USER_LOGIN table along with date & time.
|
Password management improvements
| Anchor | ||||
|---|---|---|---|---|
|
The password management improvements are comprised of four new features.
- Account lockout
- Mandatory password change
- Prevent repeat passwords
- Enforce complex passwords
Account Lockout
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-287
Accounts are locked and users are not able to sign into the i2b2 after a specific number of failed login attempts have been made.
Highlights
- Account lockout threshold and wait time is defined by the site Administrator.
- Users are locked-out when the defined number of failed attempts have been reached
- Once locked
- user receives a lockout message
- the user must wait a preset period of time
- Successful login resets the number of failed logins
New Parameters
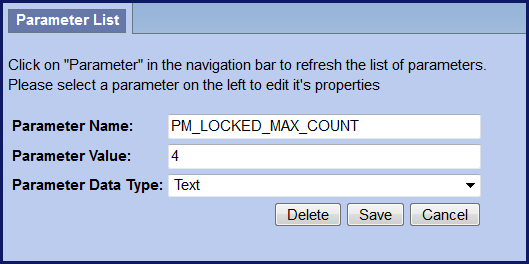
Two new Global Parameters were created as part of the new lockout feature. These parameters must be defined in the PM_GLOBAL_PARAMS table for users to be locked out after the defined number of failed attempts and number of minutes they must wait before attempting to try again.
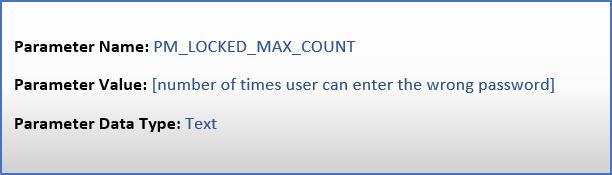
PM_LOCKED_MAX_COUNT Parameter
| Anchor | ||||
|---|---|---|---|---|
|
- Threshold for failed sign-in attempts
- The value is inclusive. i.e. if you enter 4 then the 4th time the user enters the wrong password they will receive the error message and their account will be locked.
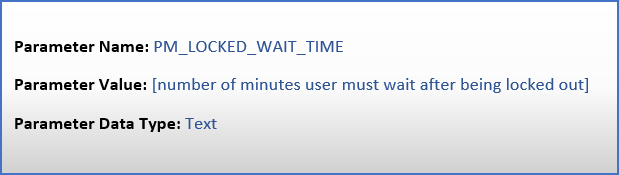
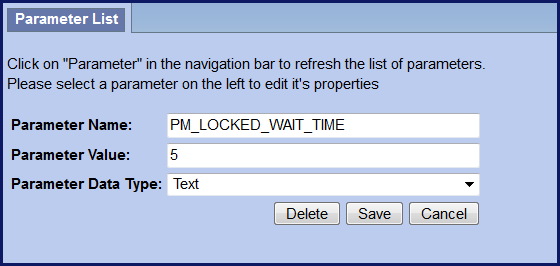
PM_LOCKED_WAIT_TIME Parameter
| Anchor | ||||
|---|---|---|---|---|
|
- Number of minutes an account is locked before a user can sign in again.
Mandatory Password Change
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-287
Require users to change passwords after a specified interval of time. The i2b2 Administrator controls the number of days allowed before a password must be changed. If a user attempts to sign on after their password has expired, the i2b2 Change Password window will open and the user must change their password before they can sign on.
Highlights
- Require users to change passwords
- i2b2 Admins control how often (interval)
- Change password window will open when password expired
- 1 new Global parameter
- 1 new User parameter
The system uses the value in the global parameter to calculate the next expiration date and adds the appropriate user parameter to the table.
Summary of password expiration process
| UI Steps | ||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| ||||||||||||||
|
New Parameters
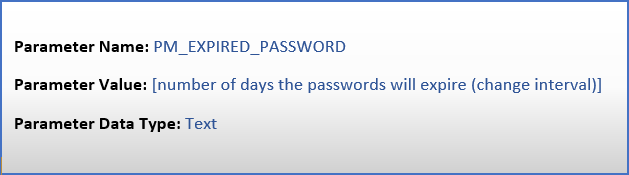
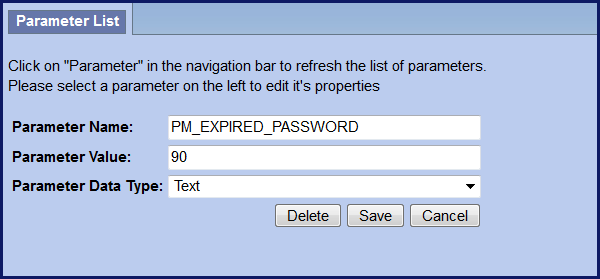
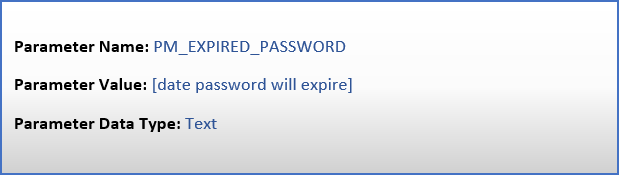
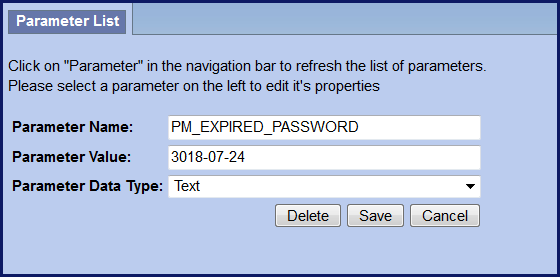
Two new parameters were created as part of the Mandatory password change feature. Both parameters are called PM_EXPIRED_PASSWORD however one is set within PM_GLOBAL_PARAMS and the other within PM_USER_PARAMS. Each parameter has a different function in the password expiration process and is further defined below.
Table: PM_GLOBAL_PARAMS
The new Global Parameter called PM_EXPIRED_PASSWORD must be added to the PM_GLOBAL_PARAMS table to define the password change interval. Once this parameter has been set the mandatory password change feature will be turned on. If this parameter is not added as a global parameter then passwords will never expire.
Highlights
- Global Parameter PM_EXPIRED_PASSWORD
- Turns the feature on
- Defines password change interval
- Affects ALL users
Table: PM_USER_PARAMS
The new User Parameter, PM_EXPIRED_PASSWORD, is automatically added to the PM_USER_PARAMS table the first time a user successfully changes their expired password. When they change their password, the system will look to the PM_EXPIRED_PASSWORD parameter in the PM_GLOBAL_PARAMS table to see the change interval defined and then calculate the new expiration date to add to the user parameter.
Highlights
- User Parameter PM_EXPIRED_PASSWORD
- Date password will expire for user
- Added by system when password changed 1st time
- Can be manually added / edited to a future date for user accounts don't want to expire
| UI Text Box | ||
|---|---|---|
| ||
As soon as you add the PM_EXPIRED_PASSWORD to your PM_GLOBAL_PARAMS table, ALL passwords will expire except the i2b2 AGG_SERVICE_ACCOUNT. To prevent service accounts from expiring you need to add the user parameter as soon as the feature is turned on or even before it. Set the expiration date for a date in the distant future. The following steps outline how to do this.
|
| UI Text Box | ||||
|---|---|---|---|---|
| ||||
Notice in the example provided above, the year was set to 3018. By manually setting the expiration date this far in the future will prevent the password from expiring and thus triggering the system to calculate the next expiration date and automatically update the user parameter. |
Prevent repeat password
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-300
Prevent users from using their current password as their new password when required to change it.
Highlights
- No additional setup is needed
- New password can't be same as current password
- Warning message displayed if user enters same password
Enforce Complex Passwords
| Anchor | ||||
|---|---|---|---|---|
|
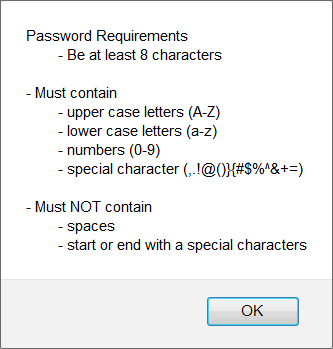
JIRA Issue: CORE-288
Enforce complex passwords
Passwords must meet complexity requirements defined by the i2b2 Administrator. The requirements will be enforced when users change their passwords. They are not enforced when the i2b2 Administrator first enters their password from within the i2b2 Admin Module.
Highlights
- New global parameter
- i2b2 Administrator defines requirements for complexity
- Enforced when users change passwords
- Warning message if don't meet requirements
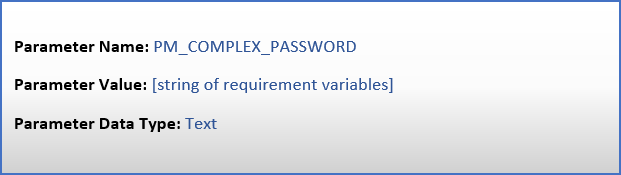
New parameter
A new Global Parameter was created to support the Enforce Complex Passwords feature. The new parameter is set within PM_GLOBAL_PARAMS table and will define the password complexity requirements. Once the parameter has been entered the feature will be turned on and all users will be required to follow the new requirements the next time they change their password. The only exception is when the password is set by the i2b2 Administrator from within the i2b2 Admin Module.
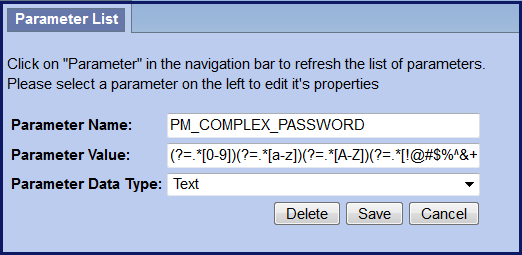
Global Parameter: PM_COMPLEX_PASSWORD
Each requirement as an independent variable however they are concatenated and stored as a single "value" in the table.
Complex Requirement Variables
When setting the parameter value for PM_COMPLEX_PASSWORD, each requirement is defined as an independent variable that is stored as a string in the VALUE column of the PM_GLOBAL_PARAMS table. The table shown below lists each of the variables and the associated requirement that will be enforced.
| Variables | Requirement |
|---|---|
| (?=.*[0-9]) | Numbers (0-9) |
| (?=.*[a-z]) | Lower case letters (a-z) |
| (?=.*[A-Z]) | Upper case letters (A-Z) |
| (?=.*[!@#$%^&+=]) | Special characters (!@#$%^&+=) |
| (?=\S+$).{8,} | Password is a string and must be 8 characters |
The requirements can be used in any combination. If all the requirements in the table were to be used, the following would be entered as the Parameter Value:
(?=.*[0-9])(?=.*[a-z])(?=.*[A-Z])(?=.*[!@#$%^&+=])(?=\S+$).{8,}
| UI Text Box | ||||
|---|---|---|---|---|
| ||||
The (?=\S+$).{8,} variable is always required when setting the PM_COMPLEX_PASSWORD parameter. The system needs to know that password is a string and the length of password. You do have the option to change the length to be greater or lesser than 8 characters. |
Query improvements
| Anchor | ||||
|---|---|---|---|---|
|
Two new features are included in the query improvements category.
- SQL Query Breakdown
- Custom breakdowns based on SQL query
- 4 new breakdowns provided in the demo data as examples
- Temporal Query made simple
- New simple mode available
- Streamlined
SQL Query Breakdowns
| Anchor | ||||
|---|---|---|---|---|
|
New breakdowns based on SQL Query
Can now have custom breakdowns based on SQL Query
Four examples provided with the i2b2 demo software
Length of stay breakdown
Top 20 medications breakdown
Top 20 diagnoses breakdown
Inpatient and outpatient breakdown
Example
Take a look at the Length of stay breakdown provided with the demo data.
SQL defined in QT_BREAKDOWN_PATH table
INSERT IMAGE of TABLE
| Code Block | ||
|---|---|---|
| ||
SELECT length_of_stay AS patient_range, COUNT(DISTINCT a.PATIENT_num) AS patient_count FROM visit_dimension a, DX b WHERE a.patient_num = b.patient_num GROUP BY a.length_of_stay ORDER BY 1 |
Run a query for all diagnoses
Temporal Query made Simple
| Anchor | ||||
|---|---|---|---|---|
|
- Temporal query interface difficult to use
- Hard to comprehend temporality
- Hard to remember population constraint
- Too complicated, difficult to learn
- 1.7.10 includes a Simple Temporal Query mode
- Displays ordering of events
- Displays population constraint
- Streamlined features
Miscellaneous improvements
| Anchor | ||||
|---|---|---|---|---|
|
Single sign-on location for Web Client and Admin Module
| Anchor | ||||
|---|---|---|---|---|
|
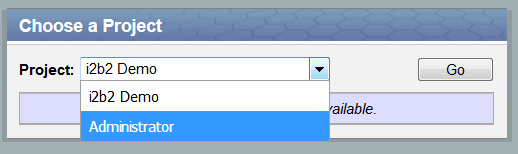
JIRA Issue: WEBCLIENT-226
The i2b2 Admin module no longer needs to be setup on the i2b2 server and results in the following benefits.
- i2b2 Administrators will log in from the same location as the i2b2 Web Client.
- Easier installation and maintenance. Will only install the i2b2 Web Client.
To sign into the i2b2 Admin module, Administrators will go to the same location as their i2b2 Web Client and enter their login credentials. Provided their user is setup as an Admin they will be able to select "Administrator" from the list of projects in the project dialog. The Administrator project will launch the Admin module.
INSTALLATION INSTRUCTIONS
Improve datasource validations
| Anchor | ||||
|---|---|---|---|---|
|
JIRA Issue: CORE-129
The On certain occasions a database connection in a pool would go bad and the i2b2 would continue to use the connection which would cause errors in the i2b2. To resolve this problem database connections will now be validated and checked that it the connection is a valid connection. If a connection in the pool goes bad we the i2b2 will not continue to use that validation.
- Validate database connection
- If connection in pool goes bad will not continue to use
using it.
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
<validation>
<validate-on-match>true</validate-on-match>
<check-valid-connection-sql>SELECT 1 FROM DUAL</check-valid-connection-sql>
<use-fast-fail>true</use-fast-fail>
</validation> |
| Include Page | ||||
|---|---|---|---|---|
|